
Regardless of your broader objectives, keeping your device healthy is a critical first step down the path toward better security. So, before you begin worrying too much about strong passwords, private communication and secure deletion, for example, you need to make sure that your computer is not vulnerable to or plagued by malicious software, often called such as viruses and spyware. Otherwise, it is impossible to guarantee the effectiveness of any other security precautions you might take. After all, there is no in point locking your door if the burglar is already downstairs, and it doesn't do you much good to search downstairs if you leave the door wide open.
Hackers are constantly breaking into innocent websites and using them to infect visitors with malware, lure them to dodgy sites and infiltrate databases to grab sensitive customer information. But you can avoid trouble -- or eliminate it quickly -- by taking some relatively simple steps.
Proof your web application –Some suggested general "best practices" from this source include:
- Change passwords frequently (outdated by today's technology)
- Don't click on email links -- type the URL in manually
- Disable the preview pane in all inboxes
- Read email in plain text
- Don't open email attachments
- Don't enable Java, JS, or particularly ActiveX
- Don't display your email address on your web site
- Don't follow links without knowing what they link to
- Don't let the computer save your passwords
- Don't trust the "From" line in email messages
- Upgrade to latest security levels particularly for Internet Explorer
- Consider switching to Firefox or Chrome
- Never run a program unless it is trusted
- Read the User Agreement on downloads (they may sell your personal data)
- Expect email to carry worms and viruses.
- Just say no to Pop-Ups
- Say no if an application asks for additional or different authorities
- Say no if it asks to read or edit anything more than a Desktop folder
- Say no if it asks for edit authority on other stuff
- Say no if it asks for read authority on odd stuff, with a connection to the Web
- During an Application Install supply a new name and new icon and a new folder path.
- Say no when anything asks for Web access, beyond 1 a specific site
- Always say No unless you want to be hit sooner or later
Keep your software up to date.
Hackers aggressively target security flaws in popular Web software such as content management systems and blogging programs so they can attack websites en masse. Stay out of the line of fire by using the latest versions of software and applying security patches promptly.
"Sites that get infected and clean up, but don't fix the vulnerability in their software, just get re-infected," says Lucas Ballard, a software engineer with Google's Safe Browsing team. He urges webmaster to address the underlying weakness that enabled the hack, as well as remove hackers' malicious code from site pages.
Use strong passwords and keep them safe.
Using strong passwords is crucial because hackers frequently attempt to crack or steal passwords for web software and FTP servers, which are computers that use the File Transfer Protocol to move web pages and other files to another computer, such as a Web-hosting server. Default, common or predicable passwords can be easily broken.Also make sure to protect your PCs from a virus infection since that can lead to the theft of site passwords.
Hackers have a lot of choices for attack vectors, but here are the 4 most common things they try first:
- Carry out SQL injection attacks to gain access to the database, spoof a user’s identity, and destroy or alter data in the database. SQL injection occurs when malicious SQL statements are inserted into form fields to try and gather information from the database. This information enables the hacker to access, modify or destroy information in the database. With SQL injection, a hacker can change the price of a product, and gain customer information such as credit cards numbers, passwords and contact information.
- Use Cross-Site Scripting (XSS)attacks to have browsers execute their malicious payloads to deface your website to promote their brand or their hacktivist ideals . XSS occurs when malicious code is injected into an application that executes on the client side.
- Make the site temporarily unavailable with a Distributed Denial of Service Attacks (DDoS). DDoS attacks generate requests from thousands of IP addresses in an attempt to flood a site with traffic, making it impossible for the server to respond to requests. DDoS attacks or bots can slow a site down or make it temporarily unavailable.
- Hijack trusted user sessions to make unwanted purchases on behalf of users with Cross Site Request Forgery (CSRF)attacks. CSRF attacks occur when a user is tricked into clicking a link or downloading an image that executes unwanted or unknown actions on an authenticated user session.
How Should You Protect Your Assets and Users?
There are different methods and tools that modern web application developers use to protect their website. There are solutions that exist for specific attacks, and best practices that can be used on an on-going basis to protect your applications and users. Code reviews, bug bounty programs and code scanners should be implemented throughout the application lifecycle. Code reviews can help spot vulnerable code early in the development phase, dynamic and static code scanners can do automatic checks for vulnerabilities, and bug bounty programs enable professional pen testers to find bugs in the website.Even with these best practices in place, you may still find yourself under attack.
Attack-specific solutions include:
1.Using stored procedures with parameters that are automatically parameterized.
2.Implementing CAPTCHA or prompting users to answer questions. This ensures that a form or request is being submitted by a human and not a bot.
3.Use a Web Application Firewall(WAF) to monitor your network and block potential attacks.
None of these methods can replace the other one – each brings its own value to the table and adds protection against certain attack scenarios. You cannot find all vulnerabilities by code reviews or bug bounty programs, nor by a web application firewall alone; no tool is 100% complete. A combination of all of these must be used to protect your application and users.
For more information about web applications against hacking and malware, please drop an Email to:info@oditeksolutions.com
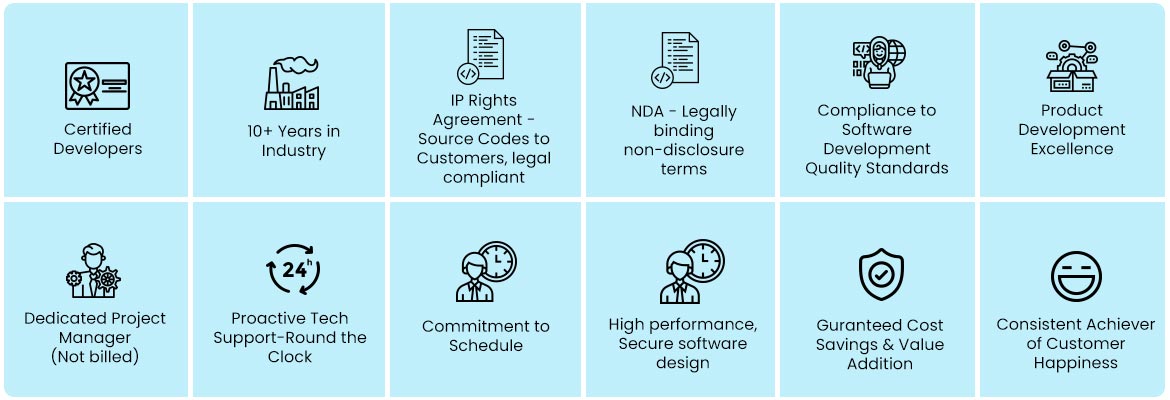
What OdiTek offers
Refer our Skills page:
Proofing your web applications against hacking and malware infections
Regardless of your broader objectives, keeping your device healthy is a critical first step down the path toward better security. So, before you begin worrying too much about strong passwords, private communication and secure deletion, for example, you need to make sure that your computer...
more












